Introduction
What is credential stuffing? Credential stuffing is a cyberattack where hackers use stolen usernames and passwords from data breaches to try logging into many accounts automatically. Credential stuffing is a type of cyberattack where hackers use stolen usernames and passwords to gain unauthorized access to online accounts. Because many people reuse the same login credentials across multiple websites, attackers can automatically test stolen credentials on different platforms until they find accounts that work.
Understanding what credential stuffing is can help users recognize how these attacks happen and learn how to protect their online accounts from unauthorized access. Understanding what is credential stuffing is can help users protect their online accounts from automated hacking attacks.
Table of Contents
How Credential Stuffing Works
Credential stuffing attacks rely on automation. Hackers obtain large databases of stolen login credentials from previous data breaches and use automated scripts to test those credentials on many websites. Many cybersecurity experts warn that what is credential stuffing attacks are increasing because people reuse the same passwords across multiple websites.
Understanding what is credential stuffing is helps users recognize how attackers exploit stolen login credentials to break into accounts. Understanding what is credential stuffing is helps users recognize how attackers use stolen login credentials to access online accounts.
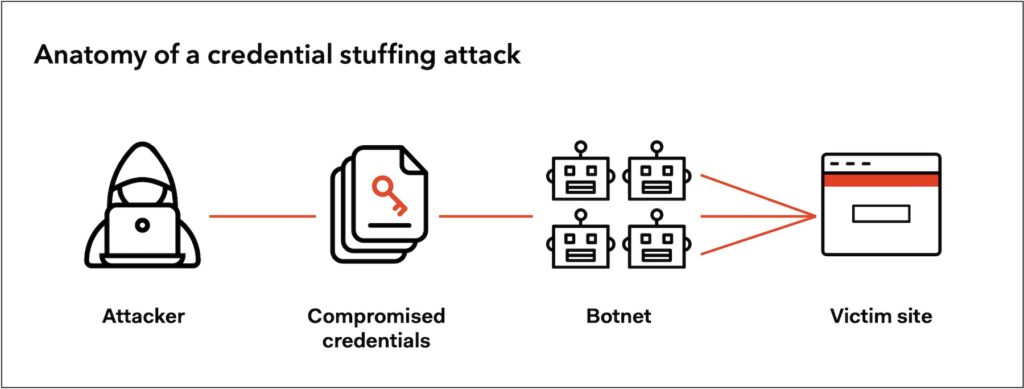
A typical credential stuffing attack follows these steps:
- Hackers obtain leaked usernames and passwords from data breaches.
- Automated bots attempt to log in to websites using those credentials.
- If the same password was reused on multiple sites, attackers gain access.
- Compromised accounts may then be used for fraud, spam, or identity theft.
Because these attacks are automated, thousands of login attempts can occur within minutes. Many attackers also use malware such as Remote Access Trojan (RAT) malware to gain control of devices and steal login credentials.
Why Credential Stuffing Is So Effective
Credential stuffing works mainly because many users reuse the same passwords across multiple services.
For example:
- A user creates an account on a small website.
- That website experiences a data breach.
- The stolen credentials are leaked online.
- Hackers use those credentials to try logging into other accounts like email, banking, or social media.
If the same password is reused, attackers may gain access instantly. If you notice suspicious activity on your device, it may help to check the warning signs your webcam has been hacked.
This is why cybersecurity experts strongly advise using unique passwords for every account.
Credential Stuffing vs Brute Force Attacks
Although credential stuffing is similar to other hacking techniques, it is different from brute force attacks.
| Attack Type | Description |
|---|---|
| Credential Stuffing | Uses stolen username and password combinations |
| Brute Force Attack | Attempts many password guesses to crack an account |
| Password Spraying | Tests common passwords across many accounts |
Credential stuffing is particularly dangerous because attackers already have real passwords from previous data breaches.
Signs Your Account May Be Targeted
Sometimes users may notice suspicious activity if their accounts are affected by credential stuffing.
Common warning signs include:
- Login alerts from unknown devices
- Password reset emails you did not request
- Unusual account activity
- Messages sent from your account without your knowledge
If you notice these signs, you should immediately change your passwords and review your account security settings.
If you’re unsure whether your account is compromised, check out our guide on signs your email has been hacked.
How to Protect Yourself from Credential Stuffing
Use Strong, Unique Passwords
Using different passwords for each account prevents attackers from accessing multiple services with the same credentials.
Many attacks rely on weak passwords, so understanding how hackers crack weak passwords can help you stay protected.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of protection by requiring a second verification step.
Even if hackers obtain your password, they cannot log in without the second authentication factor.
Use a Password Manager
Password managers generate and store strong passwords securely, making it easier to maintain unique credentials for every account.
Monitor Data Breaches
Users can check whether their credentials were exposed in data breaches using online security tools.
Regular monitoring helps detect compromised credentials early.
Why Credential Stuffing Attacks Are Increasing
Credential stuffing attacks have become more common because of the large number of data breaches occurring each year. Billions of usernames and passwords have been leaked online, providing attackers with huge databases of login credentials to test. Learning what is credential stuffing is allows users to recognize suspicious login activity and secure their accounts.
As automated tools improve, attackers can attempt millions of login requests quickly, making credential stuffing a growing cybersecurity threat. Credential stuffing attacks are increasing because billions of usernames and passwords have been leaked in previous data breaches.
Attackers collect these credentials and use automated tools to test them across many websites. Because many users reuse passwords, attackers can often gain access to multiple accounts using the same login details.
Final Thoughts
Credential stuffing is one of the most common cyberattacks targeting online accounts today. By using stolen login credentials from previous data breaches, attackers can gain access to multiple accounts if users reuse passwords.
Learning what is credential stuffing is can help users strengthen their online security and prevent unauthorized account access.
Learning what credential stuffing is and adopting stronger security practices such as unique passwords and two-factor authentication can significantly reduce the risk of account compromise. According to cybersecurity guidance from CISA, using strong passwords and enabling two-factor authentication can help protect accounts from credential stuffing attacks.
Protecting your accounts starts with understanding how these attacks work and taking proactive steps to secure your login credentials.
To stay safe from cyber threats, read our complete guide on how to protect your email account from hackers, where we cover proven strategies, tools, and best practices.
FAQ About Credential Stuffing
Q: What is credential stuffing in cybersecurity?
Credential stuffing is a cyberattack where hackers use stolen usernames and passwords from previous data breaches to try logging into multiple accounts automatically.
Q: Is credential stuffing the same as brute force?
No. Brute force attacks guess passwords, while credential stuffing uses real stolen credentials.
Q: How can you prevent credential stuffing attacks?
Using unique passwords, enabling two-factor authentication, and monitoring breach alerts are effective ways to prevent credential stuffing.

Leave a Reply